On the Optimal Number of Grids for Differentially Private Non-Interactive K-Means Clustering
On the Optimal Number of Grids for Differentially Private Non-Interactive K-Means Clustering Authors: Gokularam M, Anshoo Tandon Differentially private K-means clustering enables releasing cluster centers derived from a dataset while protecting the privacy of the individuals. Non-interactive clustering techniques based on privatized histograms are attractive because the released data synopsis can be reused for other downstream tasks without additional privacy loss. …
Continue Reading
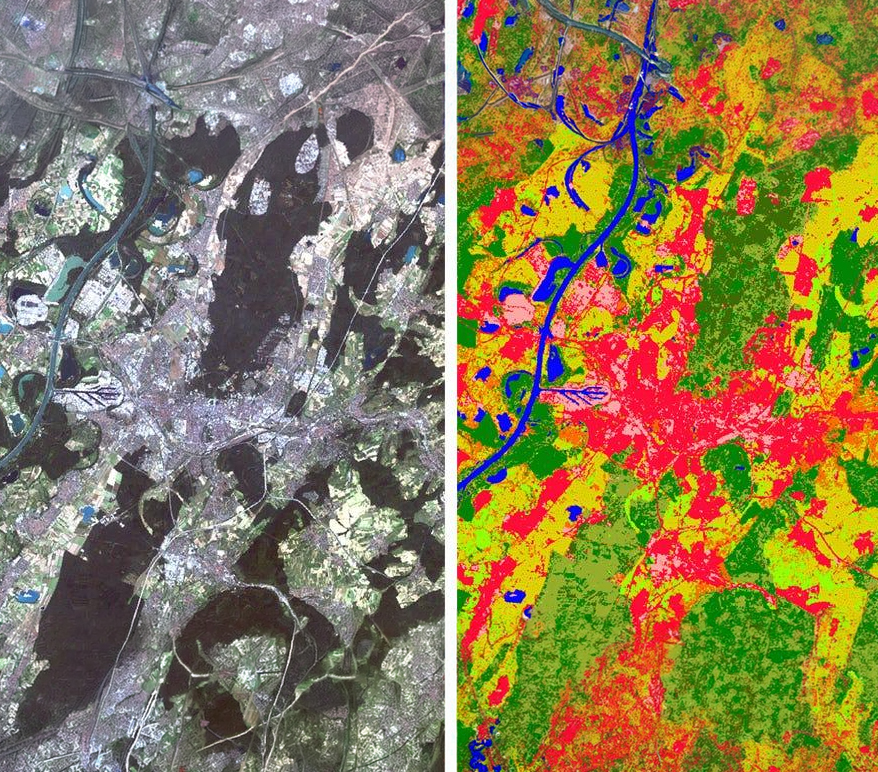
Comparison of Segmentation Methods in Remote Sensing for Land Use Land Cover
Comparison of Segmentation Methods in Remote Sensing for Land Use Land Cover Authors: Naman Srivastava, Joel D Joy,Yash Dixit, Swarup E, Rakshit Ramesh Land Use Land Cover (LULC) mapping is essential for urban and resource planning, and is one of the key elements in developing smart and sustainable this http URL study evaluates advanced LULC mapping techniques, focusing on Look-Up Table (LUT)-based …
Continue Reading
Performance Evaluation of Geospatial Images based on Zarr and Tiff
Nov 2024 Performance Evaluation of Geospatial Images based on Zarr and Tiff Authors: Jaheer khan, Swarup E, Rakshit Ramesh This evaluate the performance of geospatial image processing using two distinct data storage formats: Zarr and TIFF. Geospatial images, converted to numerous applications like environmental monitoring, urban planning, and disaster management. Traditional Tagged Image File Format is mostly used because it …
Continue Reading
SKALD: Scalable K-Anonymisation for Large Datasets
SKALD: Scalable K-Anonymisation for Large Datasets Authors:K. Reddy, N. Chakraborty, A. Dharmavaram, A. Tandon Data privacy and anonymisation are critical concerns in today’s data-driven society, particularly when handling personal and sensitive user data. Regulatory frameworks worldwide recommend privacy-preserving protocols such as k-anonymisation to de-identify releases of tabular data. Available hardware resources provide an upper bound on the maximum size of …
Continue Reading
Improving the Privacy Loss Under User-Level DP Composition for Fixed Estimation Error
Improving the Privacy Loss Under User-Level DP Composition for Fixed Estimation Error Authors:V. A. Rameshwar and A. Tandon This paper considers the private release of statistics of several disjoint subsets of a datasets. In particular, we consider the epsilon-user-level differentially private release of sample means and variances of sample values in disjoint subsets of a dataset, in a potentially sequential manner. …
Continue Reading
ℓ, 𝛿)-Diversity: Linkage-Robustness via a Composition Theorem
ℓ, 𝛿)-Diversity: Linkage-Robustness via a Composition Theorem Authors:V. A. Rameshwar and A. Tandon In this paper, we consider the problem of degradation of anonymity upon linkages of anonymized datasets. We work in the setting where an adversary links together tgeq 2 anonymized datasets in which a user of interest participates, based on the user’s known quasi-identifiers, which motivates the use of ell-diversity as …
Continue Reading
Bounding User Contributions for User-Level Differentially Private Mean Estimation
Bounding User Contributions for User-Level Differentially Private Mean Estimation Authors: V. Arvind Rameshwar (IIT Madras) and Anshoo Tandon We revisit the problem of releasing the sample mean of bounded samples in a dataset, privately, under user-level ε-differential privacy (DP). We aim to derive the optimal method of preprocessing data samples, within a canonical class of processing strategies, in terms of the …
Continue Reading
On the Optimal Number of Grids for Differentially Private Non-Interactive K-Means Clustering – Data Privacy
On the Optimal Number of Grids for Differentially Private Non-Interactive K-Means Clustering – Data Privacy Authors: Gokularam M, Anshoo Tandon Differentially private K-means clustering enables releasing cluster centers derived from a dataset while protecting the privacy of the individuals. Non-interactive clustering techniques based on privatized histograms are attractive because the released data synopsis can be reused for other downstream tasks …
Continue Reading